Lock in a year of Digiday+ for 35% less. Ends June 5.
‘Rats out of the sewers’: Ad fraudsters are leaping on the coronavirus crisis

For ad fraudsters, the coronavirus pandemic is a crisis too tempting to go to waste.
Website traffic is surging. But with advertisers adding coronavirus-related keywords to their block lists and others pausing spend altogether, ad prices on news sites are low. With less competition in the auction, low quality ads — and even publishers’ own house ads — are now making their way to the most prized ad slots on homepages. The fraudsters have quickly leaped into action.
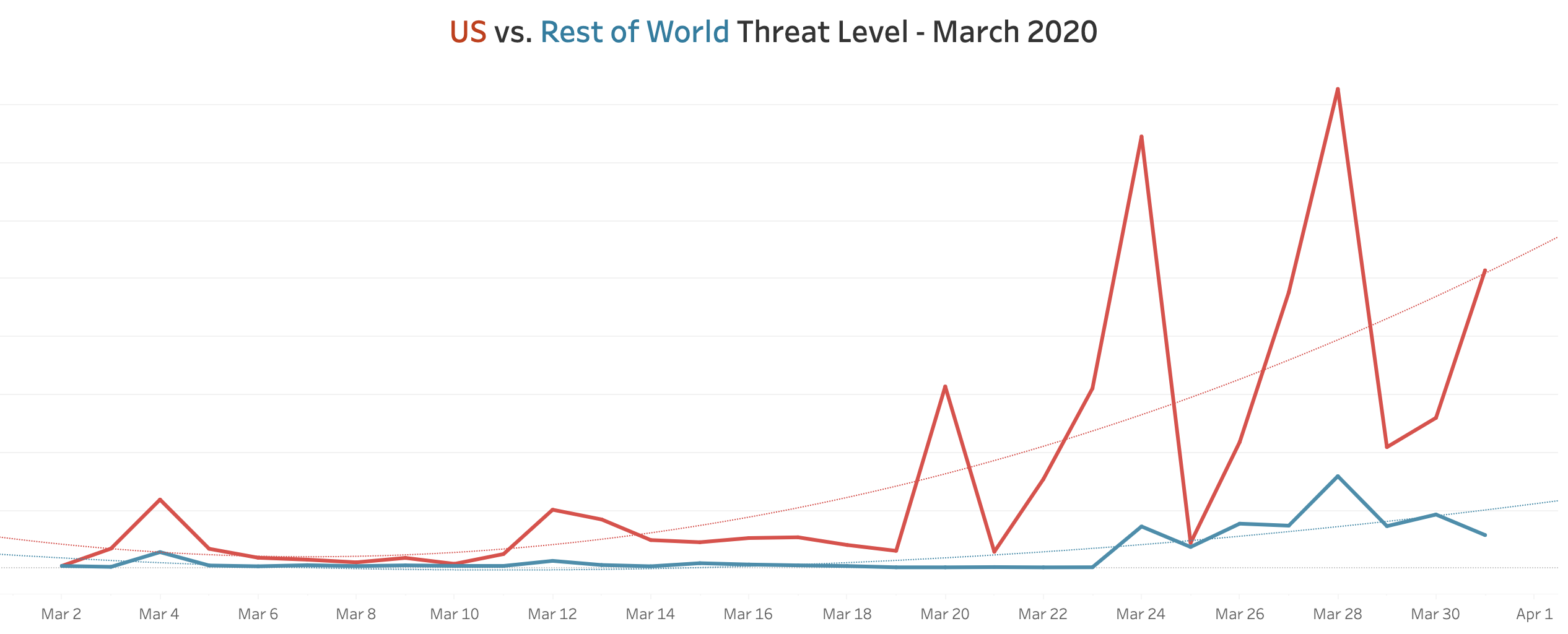
Clean.io, a company that offers malvertising protection to publishers, found there was a surge in malvertising campaigns starting Mar. 11. Clean.io’s “global threat level” — a percentage calculation of the number of threats clean.io blocked divided by the number of pageviews it behaviorally analyzed — was 50 times higher during the surge to the end of March relative to the start of the month. Around 1% of all pageviews Clean.io analyzed over the past two weeks were impacted by malicious ads, compared with a very low baseline of around 0.02% at the beginning of the month.
The U.S. has seen a significantly higher increase in malvertising compared with the rest of the world over the last month, according to Clean.io. The company said it analyzed the JavaScript within ads on tens of thousands of sites and apps that generate tens of billions of monthly page views.
The market forces of lower ad prices and extraordinarily high traffic “have basically brought the rats out of the sewers,” said Clean.io CEO Matt Gillis.
Ad fraud tends to spike over weekends and holidays as more people switch to personal devices versus work devices that tend to have better security settings. But with the majority of people now at home, there are more opportunities for bad actors to pounce.
Fraudsters have become accustomed to using sophisticated techniques to avoid being detected at the approval stage of their campaigns when they place the ads with a demand-side platform, Gillis said. Some of these bad actors have been masquerading as genuine big-name advertisers — copying the creative used in real ads from brands including Ford, Nike and Mercedes-Benz — and misrepresenting themselves as that company’s media agency of record, according to Gillis.
Continuing their efforts to evade detection, the fraudsters then sideload malicious JavaScript that only renders when it’s served on a user’s device. The fraudulent activity analyzed included click-jacking techniques to trick a user into visiting a fake landing page and auto-redirect ads informing the user they have “won an Amazon gift card” in a bid to extract their personal data. Other types of malicious activity included video stuffing, pixel stuffing, cryptojacking, and more, Gillis said.
Clean.io “saw and blocked malicious ads coming from every DSP in the ecosystem; ones you would expect have only been bringing clear demand to the market,” said Gillis. “I think there’s a misnomer that malicious ads come from low rate networks and b-rate exchanges.”
In an emailed statement, Joel Livesey, lead director of inventory partnerships at The Trade Desk, said the company has a relationship with ad verification service White Ops to block fraudulent traffic “at the door” before it enters its systems. The Trade Desk also has a range of internal systems and partners with other third-party vendors like IAS, Moat and DoubleVerify.
“This set-up works extremely well and we usually see very low single digit percentage points of fraud attempts, most of which we can root out right away,” Livesey said. “When we are concerned that fraud might have occurred, our marketplace quality team works very closely with everyone along the supply chain to follow the dollars and identify the parties involved.”
In an emailed statement, a Xandr spokesman said, “Always, and especially in these challenging times, Xandr makes proactive efforts to prevent malicious advertising in our ecosystem. We support both proprietary processes as well as partner with third-party vendors like Clean.io to monitor for and reduce malicious advertising on our platform.”
Google and MediaMath did not respond to requests for comment in time for publication.
The rise in malvertising activity is another kick in the teeth for publishers who are already taking body hits from multiple angles as the coronavirus pandemic wears on.
“Publishers are frustrated. [Malvertising] is hurting the brand, the user experience and the user is being misled,” said Jayson Dubin, CEO of Playwire, a revenue amplification platform that manages more than 450 publisher sites. “Why does it keep happening? I honestly think the onus really lies on DSPs allowing in these nefarious characters.”
Catching the criminals isn’t easy, however. The bad actors often use resellers that offer white-label versions of DSPs in order to load their ads into the marketplace, meaning they don’t need a direct seat at the original DSP themselves, said ad fraud researcher and consultant Augustine Fou. Ultimately, ad fraud is the risk publishers take on by offering their inventory to the open marketplace, he added.
“If you can shift your mix to more direct-sold and publisher-hosted ads, you reduce the percentage of ads being serviced in by programmatic sources,” Fou said. “As long as you have programmatic sources sticking ads in these slots, this problem won’t be solved.”
It’s not just advertising fraudsters hoping to turn the coronavirus pandemic into an illicit money-making opportunity. The Federal Trade Commission said on Tuesday the agency has received more than 7,800 coronavirus-related reports and that complaints spiked in the past week. Consumers reported losing a total of $4.77 million — a median loss of $598 — to coronavirus-related scams.
More in Media

Publishers quietly cut ‘six-figure’ deals via Snowflake’s AI licensing platform
Publishers are starting to make meaningful AI licensing deals via Snowflake’s RAG pipe, with some securing several six-figure deals with financial institutions.

Vox Media CRO Geoff Schiller joins Screenvision as CEO
Vox Media CRO Geoff Schiller will become CEO of cinema ad firm Screenvision, setting sights on Gen Z and a strong pipeline of movies.

Brands are getting creative as fuel costs raise shipping fees
UPS now has surge emergency fees for goods coming from India, China and Hong Kong to the United States.





