Secure your place at the Digiday Media Buying Summit in Nashville, March 2-4
Automotive, education publishers hit hard by malvertising attacks during the coronavirus crisis

Already feeling the pain from advertising pullbacks in the early throes of the coronavirus crisis, automotive and education publishers felt the brunt of malvertising attacks too.
Ad fraudsters saw the coronavirus pandemic as a prime opportunity to strike: CPMs had dropped as many advertisers paused or reduced their spend. With most people stuck inside under lockdown conditions, web traffic was surging — up 30% for news sites in March, according to Parse.ly data.
Clean.io, a company that offers malvertising protection to publishers, found that automotive publishers had the highest measure of its “global threat level” — a percentage calculation of the number of threats clean.io blocked divided by the number of pageviews it behaviorally analyzed — between April and June. A blended average of 0.28% of all automotive publisher pageviews Clean.io analyzed in the period were impacted by malicious ads. The single-day peak threat level for the category was 8.85%.
Clean.io estimated that on the worst-impacted days in the quarter, automotive sites without adequate ad fraud prevention could have lost 9% of their pageviews as user sessions were hijacked by redirects and illicit full-page takeover ads.
Automotive publishers were likely hardest hit because they saw a shortfall in ad revenue as disruption to manufacturing and fewer visits to dealerships led carmakers to slam the brakes on their digital advertising.
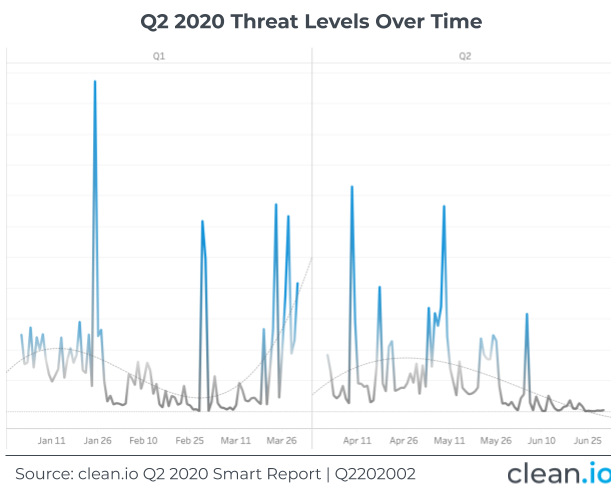
Overall, the level of malvertising observed across the 7 million websites and apps Clean.io analyzed “ebbed and flowed with with what we [saw] with [advertising] demand patterns throughout the quarter,” said Matt Gillis, Clean.io CEO. While the threat level was at its height at the beginning of April, it began petering out towards the end of May and June. That tallies the overall digital ad spending trends over the period: For most publishers, April was the bottom and revenue began ticking upwards again month-on-month in May and June.
The next most-affected group of publishers were in the education category. A blended average of 0.27% of pageviews were affected by malvertising in the quarter. The single-day peak threat level was 2.86%. In this case, Clean.io said education publishers were likely hit due to receiving huge spikes in traffic as people adjusted to the new homeschooling environment.
News sites were 20 times less likely to carry malvertising versus automotive and education sites, primarily because they are stricter about how they apply their price floors and have stricter ad-category blocks, according to Clean.io.
The majority of the malvertising occurred on mobile browsers, which is favored by fraudsters because they can take over the entire screen and masquerade as a landing page for a legitimate brand — such as an Amazon page or credit card company form — to encourage users to type in their personal information.
“That’s the reason we think mobile is the platform of choice. It’s the same reason interstitials are a good way to get people to download an application,” Gillis said.
Chrome, which commands two-thirds of the global browser market, had the biggest share of attacks in the quarter at around 36% combined across its mobile and desktop browser. Perhaps more surprisingly, Facebook’s browser, embedded within its app, had the second largest share of attacks at 29% during the period analyzed. Malvertising issues inside the Facebook browser can be harder for publishers to troubleshoot and reproduce because it is one layer removed from the usual browser experience, Gillis said.
A Facebook spokesperson declined to comment.
Catching the criminals isn’t easy as they use sophisticated methods to avoid detection, including using a wide range of demand-side platforms and resellers to carry out their attacks. In the second quarter, Clean.io observed that the bad actors also rotated around more than 60 supply-side platforms, both large and small.
A spokesman for PubMatic said the company had seen a 100-200% increase in malvertising ads between March and June. However, the spokesperson added, the company had technology and 24-hour monitoring in place to protect publishers.
“Fortunately, we have restrictive bidding in place for most of our publishers. This means we only include good creatives in auctions and exclude those awaiting classification,” said the spokesperson.
A spokesperson for OpenX said they hadn’t witnessed a rise in the number of malvertising cases between last quarter and the beginning of this year.
“It’s been standard practice at OpenX to scan 100% of the ads that run through our exchange with multiple third-party malware detection platforms and to rescan all ad creatives based on risk assessment to ensure our publisher partners, and their users, are protected from bad ads,” the spokesperson added.
OpenX is also a participant of TAG’s Threat Sharing Group, which enables sharing of details on malware issues across DSPs and SSPs, the spokesperson said.
“We’ve always invested in and prioritized solutions that guarantee a protected and secure exchange, and as part of these efforts, have a working relationship with Clean.io to ensure we can be 100% confident the path to our supply is protected,” said an Index Exchange spokesperson.
A spokesperson for Magnite did not provide a comment in time for publication,
Matt Cannon, chief operating officer of Venatus Media, a publisher monetization partner that works with clients in the gaming and entertainment industries, said SSPs do care about malvertising issues, but it can often be low priority. Venatus is a client of Clean.io.
“One of the biggest challenges is that the very nature of the dynamic of DSPs and SSPs and the way everything works means there’s no financial incentive for the demand side or the SSP pipes to proactively do something to fix this,” said Cannon. “It’s incredibly frustrating.”
More in Media

From feeds to streets: How mega influencer Haley Baylee is diversifying beyond platform algorithms
Kalil is partnering with LinkNYC to take her social media content into the real world and the streets of NYC.

‘A brand trip’: How the creator economy showed up at this year’s Super Bowl
Super Bowl 2026 had more on-the-ground brand activations and creator participation than ever, showcasing how it’s become a massive IRL moment for the creator economy.

Media Briefing: Turning scraped content into paid assets — Amazon and Microsoft build AI marketplaces
Amazon plans an AI content marketplace to join Microsoft’s efforts and pay publishers — but it relies on AI com stop scraping for free.





